Apple has released security updates for a zero-day vulnerability that affects every iPhone, iPad, Mac and Apple Watch. Citizen Lab, which discovered the vulnerability and was credited with the find, urges users to right away update their devices.
The technology giant said iOS 14.8 for iPhones and iPads, also as new updates for Apple Watch and macOS, will fix a minimum of one vulnerability that it said “may are actively exploited.”
Citizen Lab said it's now discovered new artifacts of the ForcedEntry vulnerability, details it first revealed in August as a part of an investigation into the utilization of a zero-day vulnerability that was wont to silently hack into iPhones belonging to a minimum of one Bahraini activist.
Last month, Citizen Lab said the zero-day flaw — named intrinsically since it gives companies zero days to roll out a fix — took advantage of a flaw in Apple’s iMessage, which was exploited to push the Pegasus spyware, developed by Israeli firm NSO Group, to the activist’s phone.
Pegasus gives its government customers near-complete access to a target’s device, including their personal data, photos, messages and site .
The breach was significant because the issues exploited the newest iPhone software at the time, both iOS 14.4 and later iOS 14.6, which Apple released in May. But also the exploit broke through new iPhone defenses that Apple had baked into iOS 14, dubbed BlastDoor, which were alleged to prevent silent attacks by filtering potentially malicious code. Citizen Lab calls this particular exploit ForcedEntry for its ability to skirt Apple’s BlastDoor protections.
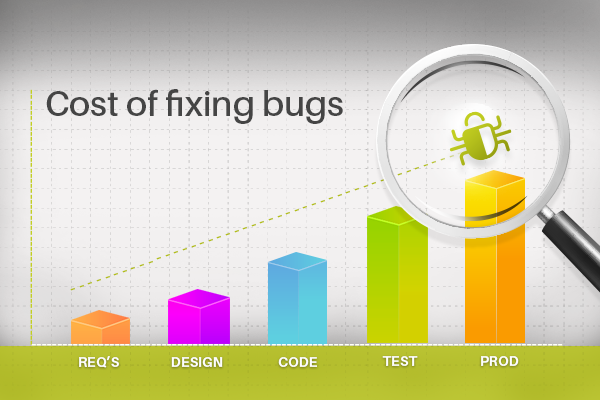
In its latest findings, Citizen Lab said it found evidence of the ForcedEntry exploit on the iPhone of a Saudi activist, running at the time the newest version of iOS. The researchers said the exploit takes advantage of a weakness in how Apple devices render images on the display.
Citizen Lab now says that an equivalent ForcedEntry exploit works on all Apple devices running, until today, the newest software.
Citizen Lab said it reported its findings to Apple on September 7. Apple pushed out the updates for the vulnerability, known officially as CVE-2021-30860. Citizen Lab said it attributes the ForcedEntry exploit to NSO Group with high confidence, citing evidence it's seen that it's not previously published.
John Scott-Railton, a researcher at Citizen Lab, told TechCrunch that messaging apps, like iMessage, are increasingly a target of nation states hacking operations and this latest find underlines the challenges in securing them.

In a brief statement, Apple’s head of security engineering and architecture Ivan Krstić confirmed the fix.
“After identifying the vulnerability employed by this exploit for iMessage, Apple rapidly developed and deployed a fix in iOS 14.8 to guard our users. We’d wish to commend Citizen Lab for successfully completing the very difficult work of obtaining a sample of this exploit so we could develop this fix quickly. Attacks just like the ones described are highly sophisticated, cost many dollars to develop, often have a brief time period , and are wont to target specific individuals. While meaning they're not a threat to the overwhelming majority of our users, we still work tirelessly to defend all our customers, and that we are constantly adding new protections for his or her devices and data,” said Krstić.